Cybersecurity doesn’t always require a massive budget or enterprise-level infrastructure. In many cases, the biggest security wins come from small cybersecurity improvements that businesses often overlook. Cybercriminals frequently exploit simple weaknesses — outdated software, weak passwords, or excessive user permissions — because they work surprisingly well.
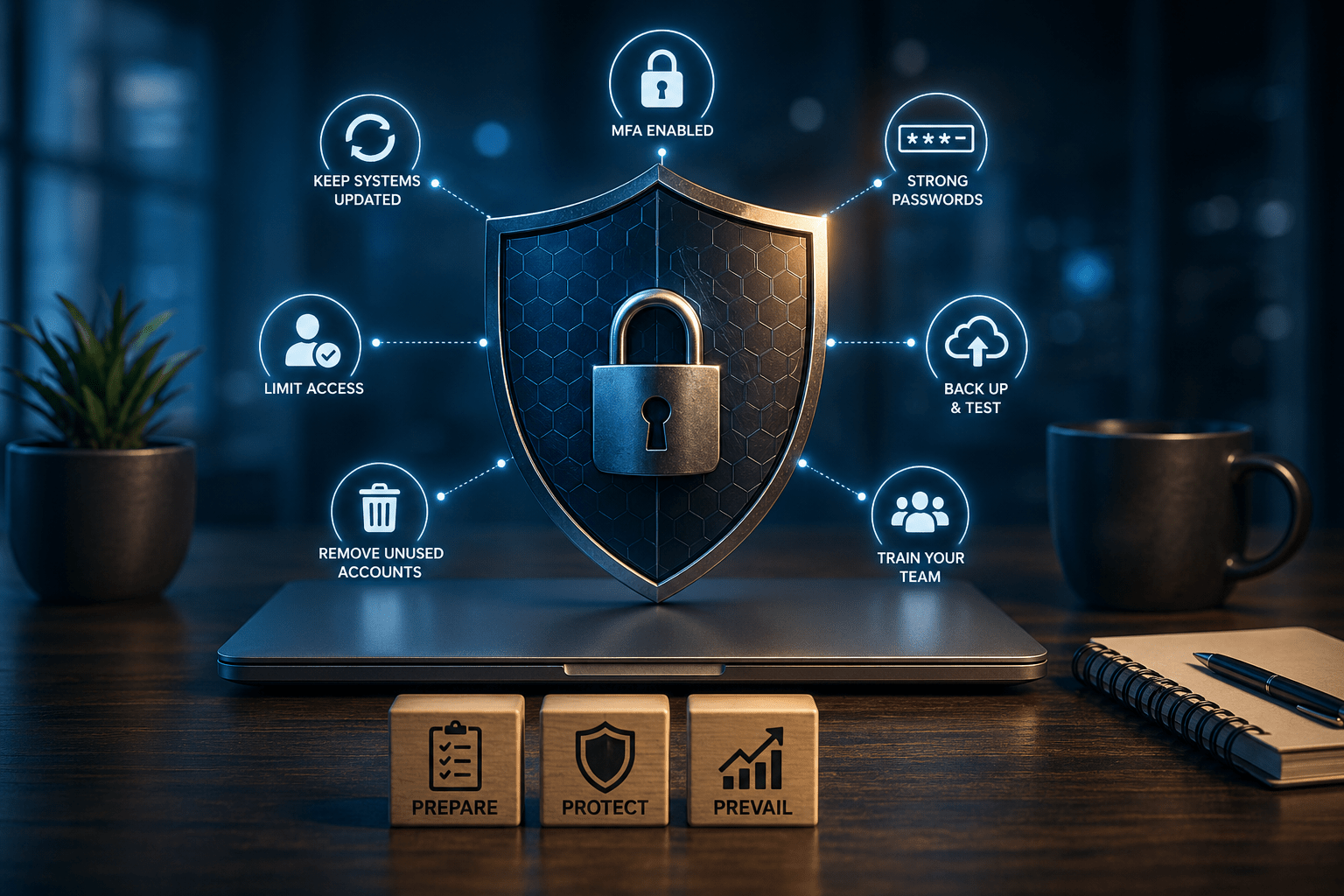
For small and medium-sized businesses, making a few strategic adjustments can dramatically reduce risk without disrupting operations. At T.RX Defense, we help organizations Prepare, Protect, and Prevail by identifying these overlooked gaps before attackers can exploit them.
Here are several simple but powerful security tweaks every business should implement.
1. Turn On Multi-Factor Authentication (MFA) Everywhere
Passwords alone are no longer enough. According to Microsoft, enabling MFA can block over 99.9% of automated account compromise attacks.
Yet many businesses only enable MFA for email accounts and forget about:
- Remote desktop access
- Cloud storage platforms
- Payroll systems
- CRM tools
- VPN access
- Administrative accounts
Every internet-facing account should have MFA enabled whenever possible.
Quick Win:
Use authenticator apps instead of SMS codes when available for stronger protection.
Learn more about how T.RX Defense helps businesses secure critical systems through our managed security services.
2. Update More Than Just Your Computer
Most people remember to update their laptops but forget about the devices connected to the network.
Attackers actively target:
- Routers
- Printers
- Security cameras
- VoIP phones
- NAS devices
- Smart office devices
The Cybersecurity and Infrastructure Security Agency (CISA) regularly warns that unpatched vulnerabilities remain one of the leading causes of successful cyberattacks.
Quick Win:
Schedule a monthly “firmware update day” for all connected devices.
Small maintenance habits can prevent massive recovery costs later.
3. Use a Password Manager
Weak or reused passwords are still one of the most common causes of breaches. Employees often reuse passwords across multiple systems because remembering dozens of credentials is unrealistic.
Password managers solve this problem by:
- Generating strong passwords
- Storing credentials securely
- Reducing password reuse
- Simplifying login management
Many modern password managers also alert users if credentials appear in known data breaches.
Quick Win:
Require unique passwords for all business systems and prohibit shared login accounts.
For businesses looking to strengthen internal policies and user training, our resource center offers practical cybersecurity guidance and best practices.
4. Limit User Access
One overlooked security issue is giving employees access to systems they don’t actually need.
This violates the principle of least privilege, which means users should only have access necessary for their role.
If a compromised account has broad permissions, attackers can:
- Access sensitive data
- Deploy ransomware
- Move laterally across systems
- Disable backups or security tools
Quick Win:
Review permissions quarterly and immediately remove access for former employees.
Simple access management dramatically reduces the impact of compromised credentials.
5. Back Up Data — And Test It
Many businesses believe they’re protected because backups exist. Unfortunately, backups are useless if they fail during recovery.
According to Veeam’s ransomware research, organizations often discover backup problems only after an attack has already happened.
A strong backup strategy should include:
- Automated backups
- Offsite or cloud storage
- Immutable backups when possible
- Regular recovery testing
Quick Win:
Test backup restoration at least quarterly.
Recovery confidence matters just as much as backup creation.
6. Train Employees to Spot Suspicious Activity
Cybersecurity technology helps, but employees remain the first line of defense.
Phishing emails continue to evolve and frequently impersonate:
- Vendors
- Executives
- Payroll departments
- Shipping companies
- Microsoft or Google alerts
Even one accidental click can create serious operational disruption.
Quick Win:
Teach employees to verify unexpected requests involving money, passwords, or sensitive data.
At T.RX Defense, we believe cybersecurity awareness is just as important as firewalls and software tools.
7. Remove Old Accounts and Unused Software
Former employee accounts and unused applications create unnecessary exposure.
Dormant accounts are especially dangerous because:
- They often go unnoticed
- Passwords may never change
- Monitoring is frequently limited
Unused software also increases the attack surface and may contain unpatched vulnerabilities.
Quick Win:
Conduct regular audits of:
- User accounts
- Installed applications
- Browser extensions
- Third-party integrations
If nobody needs it, remove it.
Small Changes Create Stronger Security
Cybersecurity isn’t always about expensive tools or complex infrastructure. Often, the most effective protection comes from improving the basics consistently.
The businesses most vulnerable to cyberattacks are usually not the ones lacking technology — they’re the ones overlooking small security habits that quietly create major risk.
By implementing these simple cybersecurity improvements, organizations can significantly reduce exposure while building stronger long-term resilience.
At T.RX Defense, we help businesses:
- Identify hidden vulnerabilities
- Improve cybersecurity posture
- Build practical defense strategies
- Strengthen business continuity planning
Ready to Strengthen Your Security?
Start with a proactive security assessment today.
- Visit: https://trxdefense.com
- Explore Services: https://trxdefense.com/services
- Resources & Guidance: https://trxdefense.com/resources
- Contact T.RX Defense: https://trxdefense.com/contact
T.RX Defense — Prepare. Protect. Prevail.